Having a secure HTTPS connection used to be a feature you’d see, for example, on banking websites, where the need to address security issues was much higher.
However, as of late, this has changed quite a bit. Part of it likely has to do with browser vendors. In the last couple of years, they’ve begun to make a point of warning you whenever you’re doing something that might not be secure. Which is a good thing.
How this is usually done is by showing you (i) an icon implying that your connection is ‘wrong’ and ‘insecure’. In reality, having SSL might not even be such a big deal if you don’t even use forms, don’t handle any passwords, or such. However, even in those cases, the browser will tell you that the site is insecure.
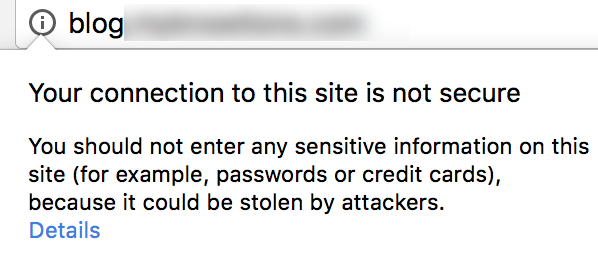
Two of the major pains that I have with certificates are the following:
- They cost money
- They expire and then I forget about them
Green Bar vs. “Normal” Certificates
Just to make things clear, we are not talking about the so-called “green bar” here (aka Extended Validation SSL Certificatese). For one of those, you’ll need to dish out $300 or more. So if what you’re looking for is how to set that up, this blog post won’t be of much help.
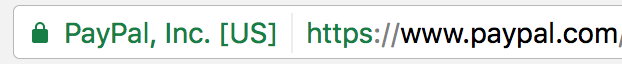
If you just want (i) to go away and have something like this, you are on the right page.

We’ll accomplish this by going through the following four steps:
- Use Let’s Encrypt
- Use custom chef script for Rails setup
- Set application env to use custom chef recipe
- Setup a cron job to auto extend certificate
Let's Encrypt
https://letsencrypt.org/ is a nonprofit Certificate Authority. For the purposes of this post, I will assume you’re running Ubuntu 14.04.4 LTS server managed with AWS OpsWorks.
In this example I’ll be adding an SSL certificate for the “kodius.com” domain.
#execute in terminal
wget https://dl.eff.org/certbot-auto
chmod a+x certbot-auto
certbot-auto certonly --standalone -d kodius.comAfter executing the previous command, a certificate will be generated inside the /etc/letsencrypt/live folder. Congrats!
If you are not using an Ubuntu/Nginx setup, then you should check out the proper command sequence here: https://certbot.eff.org/.
Tweaking nginx config
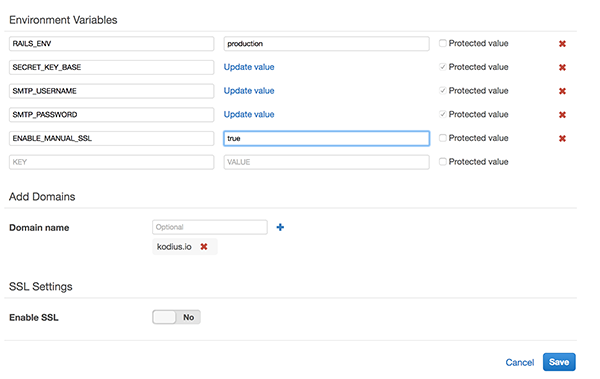
If you open up the Amazon OpsWorks console and go to your Rails app settings, you will see a section where you can manually add a certificate as well as SSL
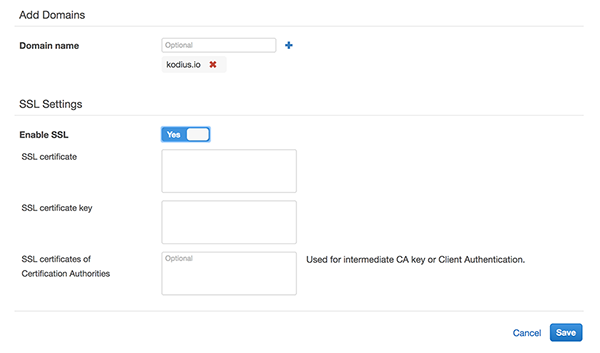
This works great, however, it requires you to manually copy/paste keys to SSL certificate input text areas. While this might not be such a big deal to do once in a while, Let’s Encrypt certificates actually run out after a mere 90 days. You might not want to do that manually.
Instead, we’ll build a custom chef script to enable SSL while the application is being deployed. We will also add a cron job to automatically extend the certificate’s validity, meaning we’ll never have to think twice about whether our certificate is going to run out.
The recipe is available here https://github.com/kodius/kodius-chef-recipes. If you are unfamiliar on how to set up a custom chef recipe on AWS OpsWorks, the setup steps are listed over here.
Edit Environment Variables inside of the Rails App
When we re-deploy the app you’ll notice nothing’s changed:
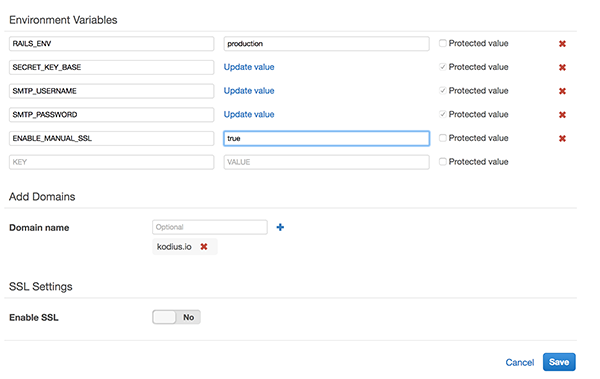
In order to make this work you’ll have to enable the “SSL” part of the recipe for setting up our nginx configuration (this part is not mandatory, so whether you want to do it or not, it’s up to you).
#setting in Rails App on OpsWorks UI
ENABLE_MANUAL_SSL = true
As shown here:
After re-deploying once more, you will get a fully set up SSL connection. The recipe we’re using puts in a bunch of redirects for nginx to the new https:// address, so old links will still work.
Setup a cron job to auto-extend certificate
Add a script /home/ubunut/renew_certs.sh
#/home/ubuntu/renew_certs.sh
#!/bin/bash
certbot-auto --quiet certonly -d kodius.com
chmod +x /home/ubuntu/renew_certs.sh
cronab -e
#add to cron
0 0 */60 * * /home/ubuntu/renew_certs.sh
Enjoy :)


